1 | function Get-DeviceCompliance { |
本脚本实现以下零信任核心检查项:
- TPM芯片启用状态验证
- Secure Boot安全启动配置
- 系统盘BitLocker加密状态
- 防病毒实时监控状态
- 系统最后更新日期
扩展建议:
- 与Azure AD条件访问策略集成
- 添加自动修复功能
- 实现实时监控告警机制
1 | function Get-DeviceCompliance { |
本脚本实现以下零信任核心检查项:
扩展建议:
PowerShell执行策略是脚本安全的第一道防线,通过灵活配置平衡功能与安全。
1 | # 查看当前执行策略 |
1 | $certParams = @{ |
1 | $signParams = @{ |
1 | # 查询脚本块日志 |
最佳实践:
1 | function Invoke-RedTeamScan { |
核心功能:
应用场景:
PowerShell 技能连载 - 零信任架构下的设备健康检查自动化
1 | function Invoke-DeviceHealthCheck { |
核心功能:
应用场景:
1 | function Invoke-DeviceHealthCheck { |
核心功能:
典型应用场景:
PowerShell 技能连载 - 软件供应链安全自动化审计
1 | function Invoke-SupplyChainScan { |
核心功能:
典型应用场景:
1 | function Invoke-ModuleVulnerabilityScan { |
核心功能:
扩展方向:
从 0day 服务器下载下来的 appz 文件夹是这样的形态:
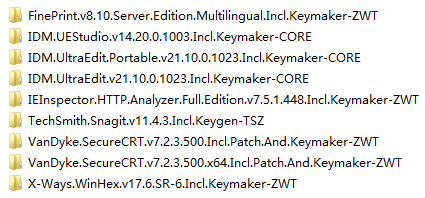
每个文件夹代表一个 appz 软件,打开是这个样子的:

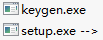
里面是一系列 .zip 文件以及说明文件。这些 .zip 文件却不是使用 zip 的分卷压缩出来的,它们的内容如下:


要把这些 .zip 文件全部解压到同一个目录下,才可以得到一系列 rar 的分卷压缩文件。我们打开一个 .rar 文件,这才看到真正的内容:
软件数量大的时候,人工重复进行上述操作就不合适了。机械的劳动应该交给程序。我们可以设计一个 PowerShell 脚本,完成一系列功能:
按照这个需求,我们可以编写如下 PowerShell 脚本:
$DebugPreference = 'Continue'
$incoming = 'd:\0day\incoming'
$temp1 = 'd:\0day\temp1'
$temp2 = 'd:\0day\temp2'
$output = 'd:\0day\output'
if (Test-Path $temp1) { del $temp1 -r }
if (Test-Path $temp2) { del $temp2 -r }
$apps = dir $incoming -Directory
$count = 0
$hasFailed = $false
$apps | foreach {
$name = $_.Name
Write-Progress -Activity 'Repacking apps' -PercentComplete ($count / $apps.Length * 100) -CurrentOperation $name
echo "Repacking $name"
md $temp1 | Out-Null
md $temp2 | Out-Null
# d:\0day\util\7z x -o"d:\0day\temp1" "d:\0day\incoming\VanDyke.SecureCRT.v7.2.2.491.Incl.Patch.And.Keymaker-ZWT\*.zip"
$arguments = 'x', "-o""$temp1""", '-y', (Join-Path $_.FullName *.zip)
.\7z $arguments | Out-Null
if (!$?) {
Write-Warning "Repacking $name failed."
echo "$name" >> "$output\fail.log"
del $temp1 -r
del $temp2 -r
$count++
$hasFailed = $true
return
}
# d:\0day\util\7z x -o"d:\0day\temp2" "d:\0day\temp1\*.rar" -y
$arguments = 'x', "-o""$temp2""", '-y', "$temp1\*.rar"
.\7z $arguments | Out-Null
if (!$?) {
Write-Warning "Repacking $name failed."
echo "$name" >> "$output\fail.log"
del $temp1 -r
del $temp2 -r
$count++
$hasFailed = $true
return
}
# copy d:\0day\temp1\*.diz d:\0day\temp2
# copy d:\0day\temp1\*.nfo d:\0day\temp2
dir $temp1 | where {
$_.Extension -notmatch 'rar|r\d*'
} | copy -Destination $temp2
#d:\0day\util\7z a "d:\0day\output\VanDyke.SecureCRT.v7.2.2.491.Incl.Patch.And.Keymaker-ZWT.zip" "d:\0day\temp2\*.*" -r
$arguments = 'a', "$output\$name.zip", "$temp2\*.*", '-r'
.\7z $arguments | Out-Null
if (!$?) {
Write-Warning "Repacking $name failed."
echo "$name" >> "$output\fail.log"
del $temp1 -r
del $temp2 -r
$count++
$hasFailed = $true
return
}
del $temp1 -r
del $temp2 -r
Remove-Item -LiteralPath $_.FullName -r
$count++
}
if ($hasFailed) {
echo '' >> "$output\fail.log"
}
echo 'Press any key to continue...'
[Console]::ReadKey() | Out-Null
# del 'd:\0day\output\*.*' -r
您也可以在这里下载写好的脚本,包括完整的目录结构和 7z 软件包。请解压到 d:\ 中使用,或者自行调整脚本头部的路径。
对于已知的需要以管理员身份运行的命令,我们可以通过这个 Invoke-Admin 函数运行。这个函数确保以管理员身份运行一个程序。如果不是以管理员身份运行,则将弹出 UAC 对话框。
function Invoke-Admin() {
param ( [string]$program = $(throw "Please specify a program" ),
[string]$argumentString = "",
[switch]$waitForExit )
$psi = new-object "Diagnostics.ProcessStartInfo"
$psi.FileName = $program
$psi.Arguments = $argumentString
$psi.Verb = "runas"
$proc = [Diagnostics.Process]::Start($psi)
if ( $waitForExit ) {
$proc.WaitForExit();
}
}
来源:Showing the UAC prompt in PowerShell if the action requires elevation